
.jpg)
Our Next Cybersecurity Webinar
Defending Your Business: Actionable Strategies to Combat Email Attacks, Ransomware, and Data Loss
Thursday, May 29th
1-2pm EST
Register Here

Download our eBook
Cyber-threats are evolving faster than ever before, and the amount of damage they can cause is increasing. To complicate matters further, nearly every industry faces constantly changing regulatory requirements. These relentless demands make it extremely difficult for a company to stay focused on its actual business.
Learn about the cybersecurity landscape SMBs currently face, the challenges, and what a more secure path forward looks like.
Download NowPrioritize Business Security
Are you confident enough in the state of your technology security, threat identification and prevention status not to worry about a breach, ransomware or cyberattack?
Our team of highly skilled professionals excels in IT consulting, delivering tailored network security services and cloud computing solutions that are designed to meet your specific needs.
We prioritize business security with robust cybersecurity solutions, including managed antivirus and anti-malware, ensuring your sensitive data is always protected.
- Secure your business, employee, and customer data
- Monitor and identify potential threats before they escalate
- Benefit from ongoing penetration and vulnerability testing to ensure maximum security
- Sleep better at night knowing your business is secure
- Increase staff security awareness

How it Works
-
Discovery Meeting
We’ll conduct a discovery meeting to understand your particular business security compliance requirements and concerns.
-
Security Assessment
Next, we’ll schedule a technical specialist to visit your location(s) and conduct a security assessment to identify gaps in your security posture that should be addressed and data that should be encrypted.
-
Dark Web Audit
We’ll identify if any of your business data, email accounts or passwords have been compromised and are available on the Dark Web.
-
Develop a Strategy
we’ll analyze it to develop a strategy to harden and secure your infrastructure, devices, platforms and services from external attacks, and continually monitor your systems for rapid threat detection. From there, we’ll put together an ongoing security awareness training and testing program to educate your staff in ways to identify and avoid electronic and socially engineered security threats.
Continuous Security Oversight
Our managed security services offer continuous oversight, 24/7/365. Attempting to handle your critical security needs yourself requires a large investment in money, manpower and security expertise. Many companies rely on an MSP to provide services but may be surprised to know they only have the very basic protections and outdated technology in place because their MSP lacks the expertise to implement a full cybersecurity solution.
The ever-changing landscape of cybercrime requires 360-degree protection. We provide a full cybersecurity platform based on the NIST Cybersecurity Framework, which is known globally as the best model to follow to prevent and respond to cyber threats.
Once we’ve agreed to engage, a security discovery meeting can be scheduled within 2 weeks. Following our discovery meeting, we’ll be able to schedule an onsite security assessment within the following week. For a typical small office, our onsite security assessments can usually be completed in 2 days.
It will take us approximately a week to analyze the information gathered during the discovery meeting and the technology assessment. We’ll be able to meet with you the following week to deliver our findings and recommendations.
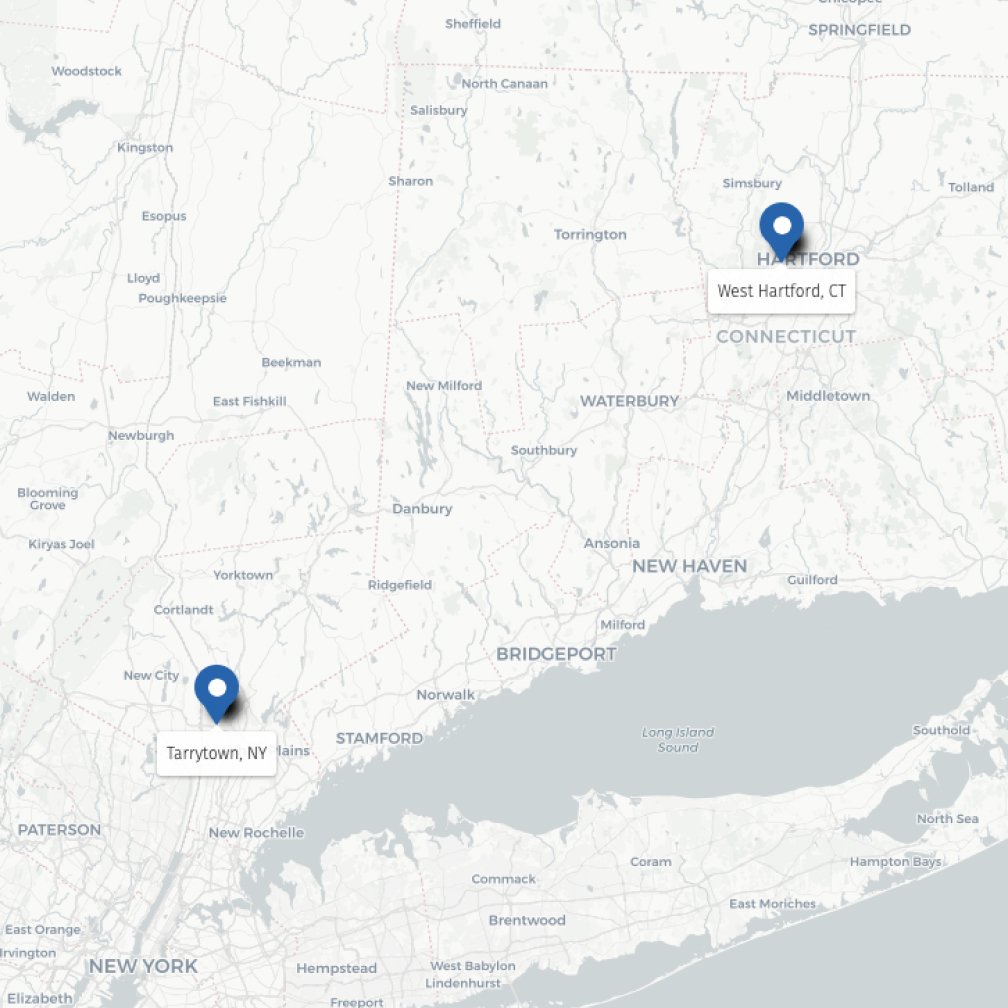
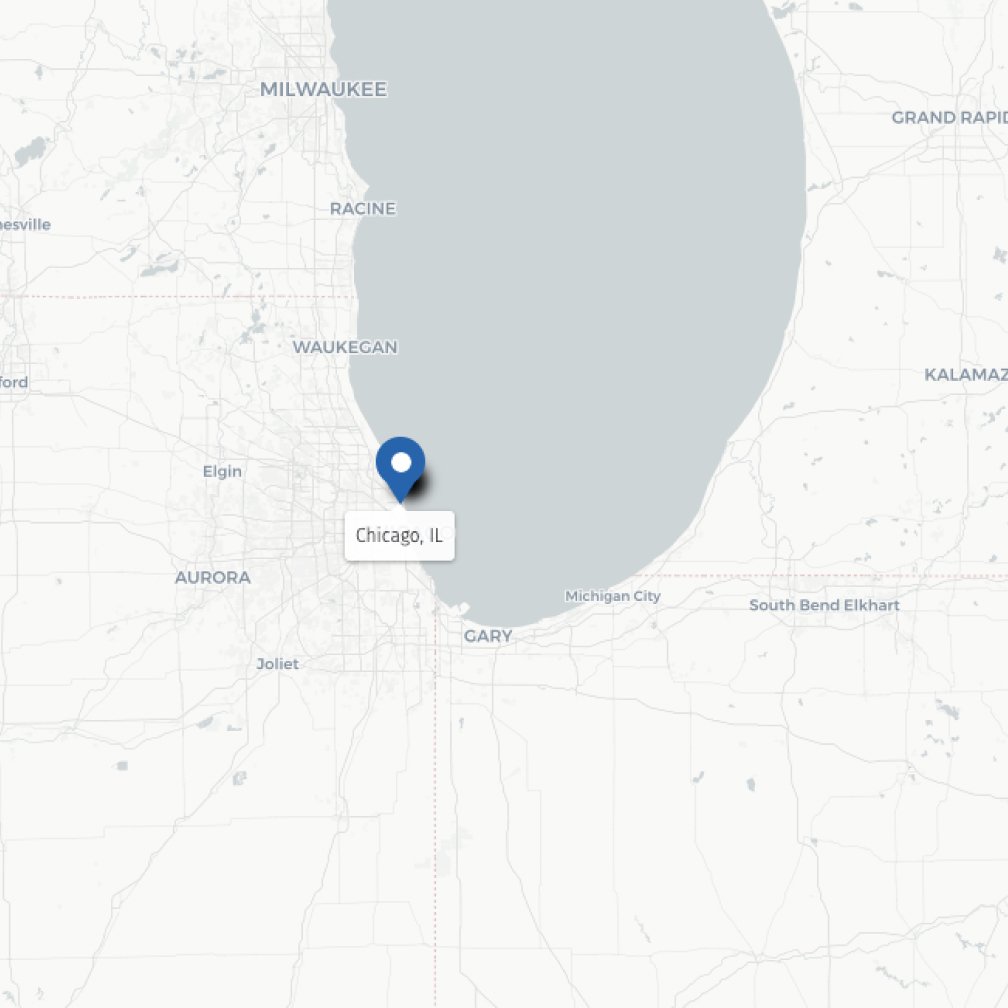
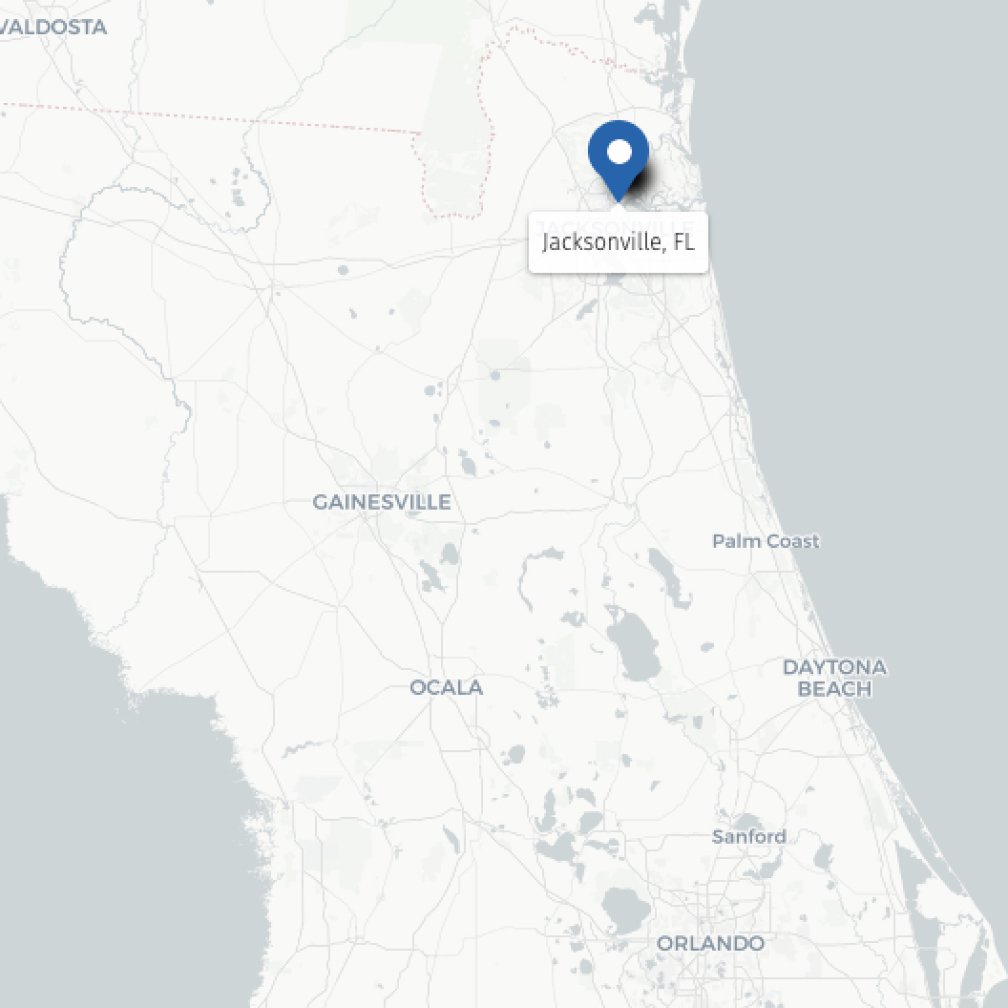
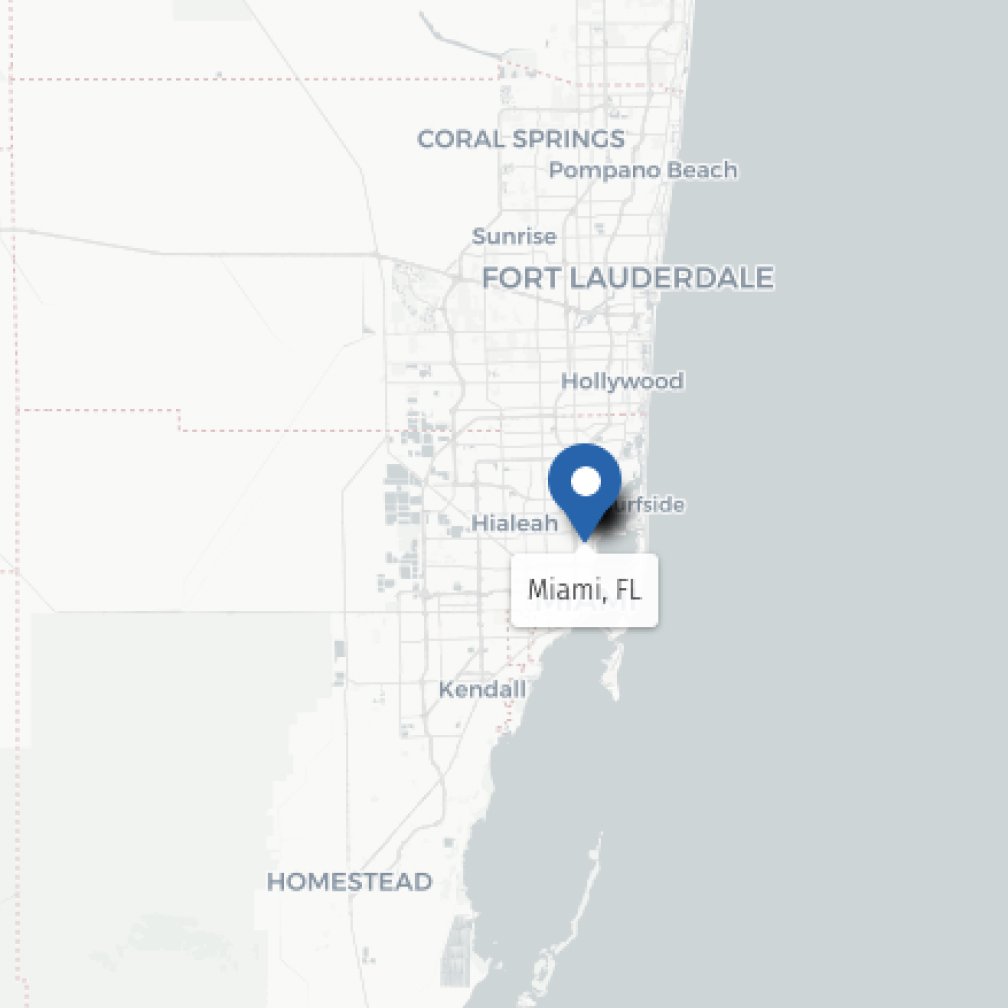
Our Locations
We serve growing small to mid-sized businesses with office locations throughout the East Coast and Midwest, in Connecticut, New York, Florida, Maryland, Pennsylvania, New Jersey, and Illinois. We offer best-of-class IT services designed to fit your needs. Find out how CompassMSP can boost your operations, improve your security, and more with our comprehensive IT managed, co-managed, and cybersecurity and compliance services.
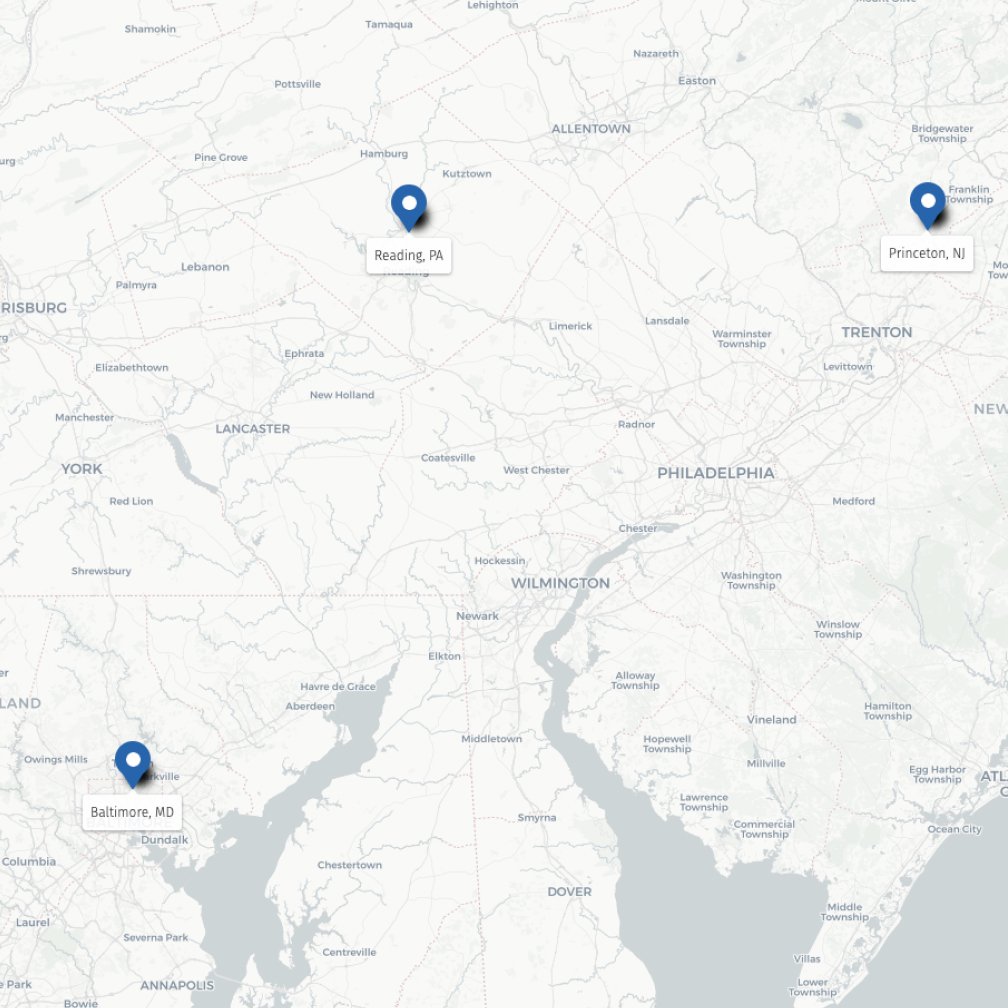
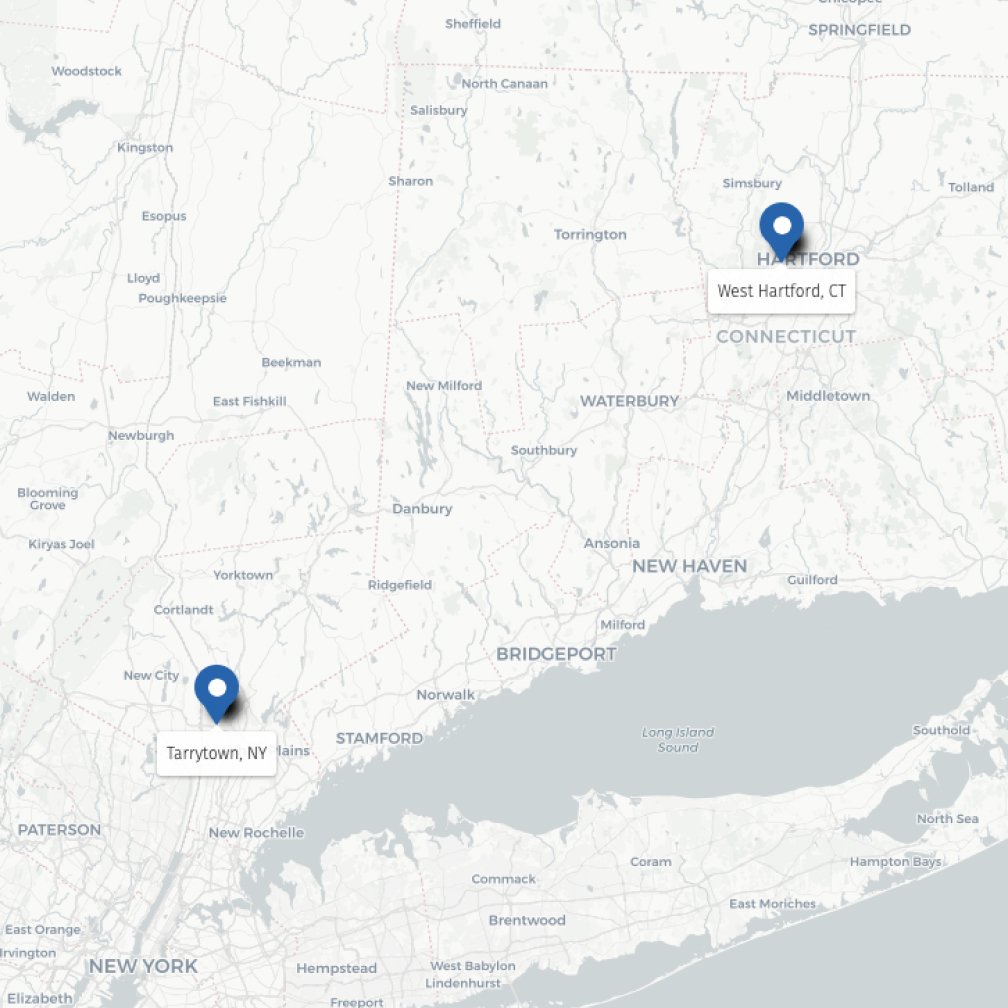
Mid-Atlantic
Northeast
Midwest
North Florida
South Florida
Recognition and Achievements
.jpg?width=124&height=124&name=Global%20Partner%20Awards%202025%20-%20Badges%20-%20Seals%20and%20eSigs%20-%20SEAL%20-%20Managed%20Security%20Partner%20of%20the%20Year%20(1).jpg)
CompassMSP Named Sonicwall's 2025 Managed Security Partner of the Year

CompassMSP Ranked in CRN's Managed Service Provider 500

CompassMSP in Inc. 5000 List of America’s Most Successful Companies
.png?width=285&height=124&name=%7B69ec4867-17da-42f5-9911-d8cd46ac5bb3%7D_2025_MSP_501_Winner_Logo_color_(1).png)
CompassMSP Listed in the Channel Partners MSP 501 Rankings

CompassMSP Named to Business Rate's 2024 Best of Computer Support and Services List

CompassMSP Named as Barracuda's MSP of the Year in 2024

CompassMSP Ranked in CRN's Tech Elite 250
.png?width=215&height=124&name=image%20(10).png)
Inc. Names CompassMSP to 2025 List of the Fastest-Growing Private Companies in the Northeast
.jpg?width=64&height=124&name=2025_CRN_SP_500_vertical%20(1).jpg)
CompassMSP Named to CRN's Solution Provider 500 List
The CompassMSP Journey
We partner with you to implement IT solutions and strategies that help you reach your business goals. With our proven process, we get to know your business and then select the right IT and cybersecurity services to best fit your needs. Here’s how we do it:
Discovery
The Discovery consultation
Where do you want your organization to be? What are your goals and what are the challenges that are holding your business back? First, we discover where you and your business are in relation to where you want to be. Only then can we begin to understand how to attain success.
Design
IT Roadmap design
Here we align your budgets with your vision to create the right set of tools that bridge the gap while elevating your business to the next level. Your roadmap will show you the system you need to simplify your work and expand your possibilities.
Implementation
Implementation
Here, we outfit your organization with the tools you need to turn your ideas into reality. We implement new processes and best practices, so you're comfortable with your system and ready to maximize your investments.
Support
Ongoing support
Communication and support are key to long-term success. Our continuous improvement process and ongoing support eliminate common day-to-day frustrations and empower your team to be more productive. Nothing falls through the cracks because CompassMSP is always behind you.
Ready to unleash your business’s full potential?
Get in touch with our team today and experience the difference a strategic IT partner can make. We’ll handle the complexities of IT, while you focus on driving your business to new heights.
Join our Mailing List!
Subscribe for updates and webinar invitations from CompassMSP.